Cybersecurity Incident Analysis
252 posts | Page 1 of 11

Cybersecurity Incident Analysis
GitHub Internal Repositories Breached via Compromised Nx Console VS Code Extension: 2026 Supply Chain Cybersecurity Incident Analysis
Cybersecurity Incident Analysis
TanStack npm Supply Chain Attack: Detailed Analysis of the May 2026 GitHub Actions Breach and Multi-Ecosystem Impact

Cybersecurity Incident Analysis
Iranian Cyberattacks Exploit Unsecured Automatic Tank Gauge Systems in US Gas Stations: 2026 Incident Analysis and Mitigation Recommendations

Cybersecurity Incident Analysis
OpenAI macOS Apps Targeted in TanStack Supply Chain Attack: Two Employee Devices Compromised, Urgent Updates Required

Cybersecurity Incident Analysis
Grafana Labs GitHub Actions Breach: Code Repositories Accessed and Extortion Attempted via Misconfigured CI/CD Workflow
Cybersecurity Incident Analysis
American Lending Center Ransomware Attack Exposes Sensitive Data of 123,158 Individuals: 2025 Data Breach Report

Cybersecurity Incident Analysis
OpenAI macOS Products Impacted by TanStack Supply Chain Attack via Mini Shai-Hulud Malware in TeamPCP Campaign

Cybersecurity Incident Analysis
Škoda Auto Online Shop Data Breach Exposes Customer Information via E-Commerce Software Vulnerability

Cybersecurity Incident Analysis
Checkmarx Jenkins AST Plugin Supply Chain Attack: TeamPCP Compromise Follows KICS Breach and Trivy Credential Theft

Cybersecurity Incident Analysis
Supply Chain Attack: Fake OpenAI Repository on Hugging Face Distributes Infostealer Malware Targeting Developers and AI Tools

Cybersecurity Incident Analysis
Poland Water Treatment Plants ICS Breached by Russian and Belarusian APTs: 2025 Attack Exposes Critical Infrastructure Security Gaps

Cybersecurity Incident Analysis
NVIDIA GeForce NOW Data Breach: Armenian Users’ Personal Information Exposed via GFN.am Partner System

Cybersecurity Incident Analysis
JDownloader Website Supply Chain Attack: Installers Replaced with Python RAT Malware (May 2026)

Cybersecurity Incident Analysis
Braintrust AWS Data Breach Prompts Urgent API Key Rotation for AI Platform Customers
Cybersecurity Incident Analysis
ShinyHunters Launches Second Major Attack on Instructure Canvas LMS via Free-For-Teacher Accounts: May 2026 Breach Analysis and Mitigation

Cybersecurity Incident Analysis
Vimeo Data Breach 2026: ShinyHunters Exploit Anodot Integration to Expose 119,000 User Records via Snowflake and BigQuery

Cybersecurity Incident Analysis
Instructure Canvas Data Breach: ShinyHunters Hack Exposes Student Information at 8,800+ Schools and Universities

Cybersecurity Incident Analysis
Instructure Canvas Cybersecurity Incidents: Analysis of 2025 Salesforce Breach and 2026 Canvas Data 2 & Beta Security Event

Cybersecurity Incident Analysis
26 FakeWallet Apps Impersonating Crypto Wallets Discovered on Apple App Store: Seed Phrase Theft Campaign Targeting iOS Users (April 2026)
Cybersecurity Incident Analysis
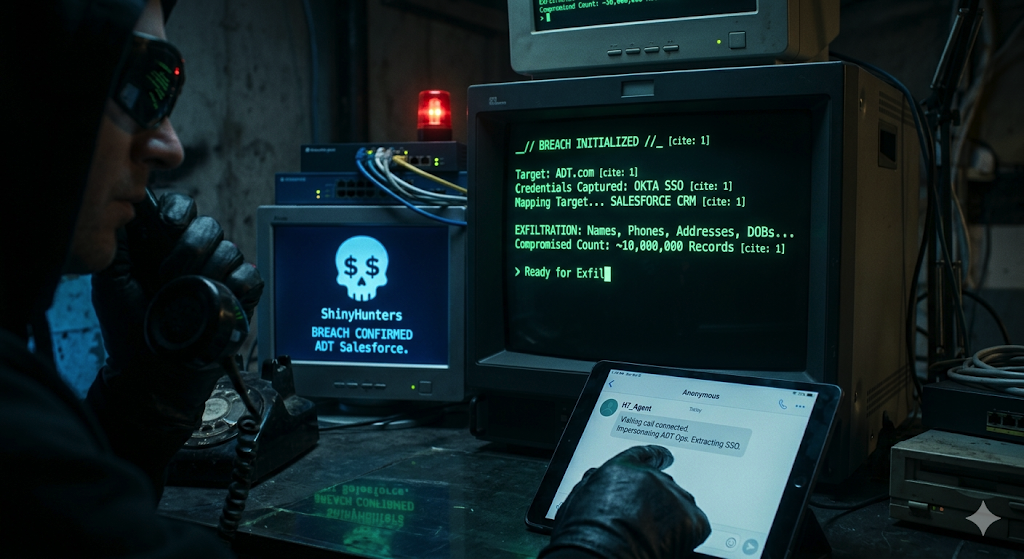
ADT Salesforce Data Breach 2026: ShinyHunters Compromise Okta SSO via Vishing Attack

Cybersecurity Incident Analysis
Vercel April 2026 Security Incident: Context.ai-Linked Breach Exposes Non-Sensitive Environment Variables and Customer Accounts

Cybersecurity Incident Analysis
JanaWare Ransomware: Six-Year Campaign Targeting Turkish Home Users and SMBs with Advanced Geo-Fencing and Evasion Techniques

Cybersecurity Incident Analysis
Critical Supply Chain Attack on EssentialPlugin WordPress Suite Exposes Over 400,000 Websites to Malware

Cybersecurity Incident Analysis